This month, we continue to be at the edge of the Internet talking about aspects of Traffic Engineering (TE) in BGP! We began our blog series by writing about TE – the what, the why, capacity management and traffic management. This month, we’re taking a look at outbound and inbound TE on the Internet, focusing on how BGP performs best path selection and some of the BGP attributes that make up the algorithm to determine the best path for packets.
Optimising traffic flow is something every good network engineer tries to achieve, and there are several ways that we can do this. An important issue that often occurs during peak times is traffic congestion. We don’t need to tell you about the issue with traffic congestion, but for end users, seeing that buffering symbol is just as disappointing as seeing the red ring of death on an Xbox! Let’s begin by looking at optimising traffic flow through the lens of outbound vs. inbound traffic.
Outbound vs inbound
As network experts, we know what outbound and inbound traffic is, so let’s skip ahead and talk about engineering it! Engineering outbound traffic is the process of manipulating the routing of traffic leaving our AS. By doing this, we can locally influence outbound traffic routes by adjusting BGP attributes, specifically local preference or AS path length. In comparison, engineering inbound traffic is much more complex and involves manipulating the routing of traffic coming onto our network. It involves adjusting the BGP attributes of routes advertised by peers, but don’t forget, peers can override these attributes when updates are sent, making it much harder. Now that we’ve covered the difference between outbound and inbound TE, let’s talk more about best path selection.
‘Okay BGP, show me the fastest route’
The BGP specification defines an algorithm known as best path selection to choose and install the best routes into routing tables. The algorithm uses a predefined set of criteria to select the most efficient route across the Internet to a destination address or prefix. The table below lists the order of criteria.
| Priority |
Attribute |
| 1 |
Local preference |
| 2 |
Local origin |
| 3 |
AS path length |
| 4 |
Origin code (lowest) |
| 5 |
MultiExit Discriminator (MED) |
| 6 |
eBGP over iBGP |
| 7 |
Shortest IGP path to BGP next-hop |
| 8 |
Oldest path |
| 9 |
Router ID |
| 10 |
Neighbour IP address (lowest) |
Now that we’ve looked at this broadly, let’s examine this a little further and look at the attributes that can be manipulated to determine the best path.
BGP attributes
BGP protocol determines a score for each path based on attributes – these are the aspects we manipulate to make the BSP algorithm work the way we want it to. To better understand attributes, let’s split them into categories: mandatory, discretionary, optional transitive and optional non-transitive.
Mandatory
Mandatory: sounds demanding, doesn’t it? That’s because they are REQUIRED for routes to be considered valid. These are recognised by all BGP peers and are present in all update messages. These attributes are Next-hop, Origin and AS Path.
Discretionary
Discretionary attributes influence the algorithm but aren’t required for route validation. These are recognised by all routers, passed to all peers and can be included in update messages if required. These attributes are Local Preference and Atomic Aggregate.
Optional transitive
Optional transitive attributes can provide additional information about routes, but don’t generally affect the algorithm. They are possibly recognised by BGP routers and may be passed to other peers when received from a peer. These attributes are Aggregator and Community.
Optional non-transitive
The optional non-transitive attributes are Multi-Exit Discriminator (MED), Originator ID and Cluster ID. Non-transitive attributes received from a peer are not permitted to be passed to other peers by the receiving AS.
In addition to attributes, asymmetric routing is also integral to quality TE.
Let’s take a different route home
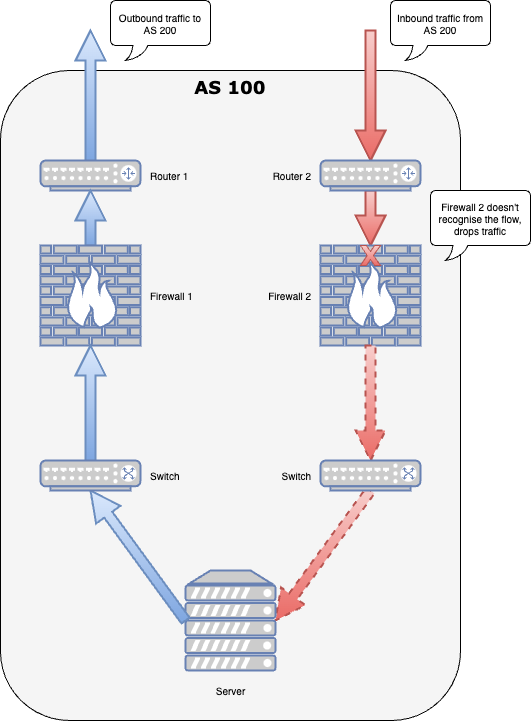
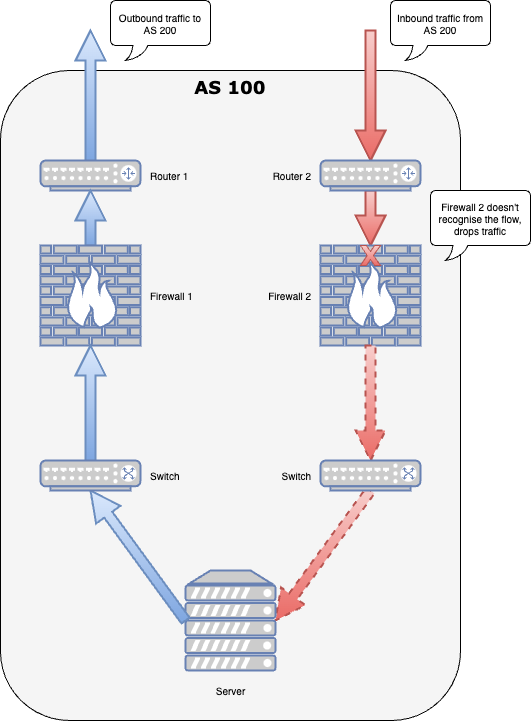
Asymmetric routing is another important aspect of TE. This occurs when a packet travels from a destination down one path and takes a different path upon its return – it’s very common in BGP and you can’t avoid it! Generally, asymmetric routing doesn’t cause issues, but when it does, it’s usually causing issues with load balancing leading to suboptimal routing. This type of routing occurs when 2 available paths are present and contain the same number of hops; AS path length will not force a routing decision. Therefore, the algorithm moves to the next attribute in the priority stack.
Asymmetric routing can also cause issues with stateful devices, such as firewalls: traffic flows returning via a different path than the one they departed on can arrive at a different device, and if the receiving device is not aware of the flow’s existence or has no matching entry in its state table, the incoming traffic is dropped:
Something’s wrong, help!
Things are always great when they work, unfortunately that’s not always the case! When it comes to TE, there are some great diagnostic tools out there including looking glasses, RIPE Atlas, NLNOG RING and more. They help us to troubleshoot a variety of different network issues. Here at IAA, we use looking glasses wherever they are available to determine how a network (AS) directs traffic destined for a particular IP address or subnet. We also operate our own looking glass for each IX, which can help give a better understanding of the paths available to a particular destination via the IX (or, indeed, if a destination is NOT reachable via the IX). When a looking glass is not available (i.e. a network operator has not made one publicly available), tools such as RIPE Atlas are invaluable for observing the path that traffic takes out of a particular AS, and can be used to narrow down the probable point of any routing issues along the path from a given AS to the destination.
Understanding the difference between outbound and inbound traffic engineering is crucial to optimising traffic flow over networks. As network engineers, understanding which attributes can be manipulated to ensure packets travel down the best path can help reduce traffic congestion, improve efficiency and reliability. If you’d like to learn more about how to improve network performance through outbound traffic engineering, stay tuned for next month’s ‘how to’ blog article!